Canada is a nation of small- and medium-sized enterprises (SMEs). They are the cornerstone of our national economy, key contributors to economic growth and a vital part of our communities. Nearly all businesses in Canada (99.8 per cent) are considered SMEs,i and organizations such as charities and non-profits are often similar in size.ii SMEs in Canada are navigating uncertainty caused by the coronavirus pandemic, but they are also facing another kind of epidemic: a rise in cyber attacks spurred by the widespread shift to remote work.
Trust is the foundation for growth and innovation in the digital era. The long‑term consequences of falling victim to a cyber attack can be severe for SMEs seeking to regain their footing after the economic fallout of the pandemic. SMEs can build organizational cultures of vigilance and risk mitigation by prioritizing cyber strategy, enhancing IT security controls, and implementing policies and procedures. These steps can also help SMEs secure data, keep costs reasonably low and increase their competitiveness.
An increasingly active cyber threat landscape
Businesses consistently rank cyber attacks as one of their top risks to growth. In fact, cyber attacks are among the top 10 risks in terms of likelihood and severity of impact in the World Economic Forum's Global Risks Report 2020. Indeed, a cyber attack is not a matter of "if", but "when", and an ever‑present concern for companies of all sizes. Without proper protections in place, companies risk monetary losses, reputational blowback, and theft of intellectual property and customer data.
SMEs caught in the crosshairs of cyber attacks
According to StaySafeOnline.org, 71 per cent of data breaches happen to small businesses, and nearly half of all Canadian small businesses have been the victim of a cyber attack.
Small businesses are one of the biggest attack targets for cyber criminals because, unlike government agencies and large corporations, they are often not as mature when it comes to their IT security, and there may be several points of entry with different employees. Further, SMEs often think they are not high‑profile enough to be targeted, and thus, they neglect investing in the cyber protections needed to prevent unauthorized intrusions.
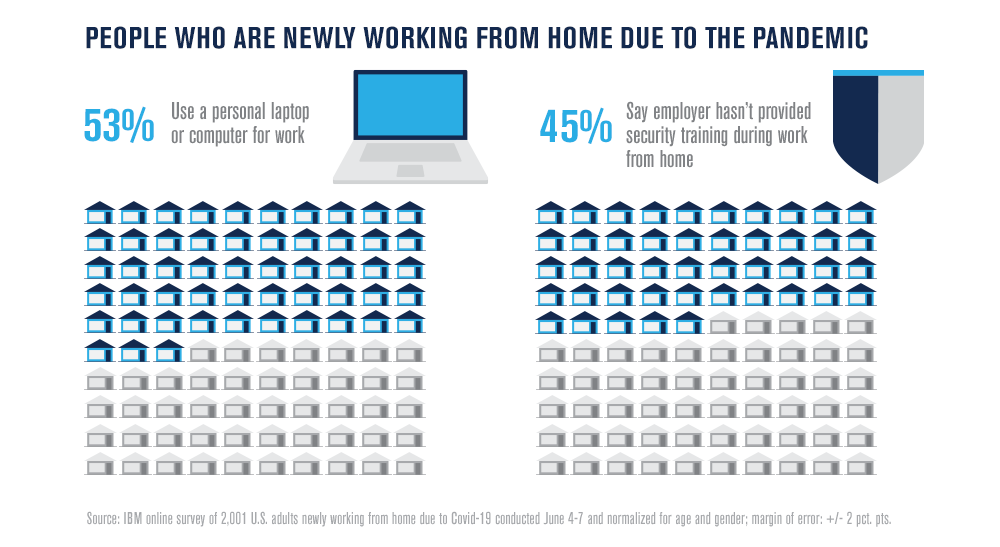
Many SMEs have shifted their employees to work‑from‑home arrangements because of the COVID‑19 outbreak, thereby introducing new security vulnerabilities and elevating their cyber risk level. The most prominent security threats include phishing, spear‑phishing, malware, ransomware, business email compromise and credential stuffing, to name a few. These attacks have proliferated during the pandemic, thus magnifying cyber security concerns for practically every organization because their employees rely on home networks. Interpol has warned that cybercrime has already spiked during the pandemic, with a further increase expected. Compounding the issue is the fact that the majority of cyber attacks trace back to human error.
A false sense of security
Smaller companies tend to overestimate the effectiveness of their cyber security because they often fail to grasp the complexity of the challenge, particularly with the shift to remote work and the difficulties around user authentication. Tied to that, many SMEs may underestimate the increasing sophistication of cyber attacks and the broad nature of modern cyber criminal campaigns that target millions of entities irrespective of an SME's activity sector. An important first step in the journey to stronger cyber defence is identifying and addressing the most common mistakes made by small businesses.
Mistake 1: Lack of a cyber security plan
One of the best defences against cyber threats to an organization is a solid cyber security plan. Astonishingly, more than 85 per cent of small businesses in Canada do not have one in place.iii Moreover, companies aren’t doing enough to limit phishing, which is the most common intrusion method.
Mistake 2: Not maintaining the technology used for cyber defence
New vulnerabilities in both software and hardware used by SMEs continue to be discovered. Businesses should regularly upgrade and patch computer systems, applications and services to address vulnerabilities and defend against ever‑evolving cyber threats. IT security professionals should familiarize themselves with new tactics and adapt their cyber strategy continuously. Moreover, the security of home networks for employees working remotely adds a new dimension for many SMEs that historically focused on defending a common physical location.
Mistake 3: Using, reusing and sharing weak passwords
Data breaches continue to occur, and, once compromised, a password associated with an SME or an individual associated with an SME, may be compiled with other passwords to access other systems. Moreover, stolen account credentials may also be used to gain unauthorized access to company systems. Companies should require that their employees use strong passwords or passphrases that are hard to guess and consider additional authentication tools to validate access credentials for employee access – particularly where remote access is involved.
Mistake 4: Relying solely on technology to protect the organization
Technology is only one arrow in the quiver. The human factor continues to be the largest variable in an organization’s cyber defence plan. Promoting a broad awareness and understanding of the cyber threat landscape across the organization is vital. Greater awareness ensures that cyber defences are not accidentally compromised by employees. The best way to counter a cyber threat is to cultivate a risk-aware workplace, which starts with cyber security awareness and training.
Foundational best practices: baseline cyber security controls for SMOs
Building strategic capabilities to enhance cyber defences does not have to be complex or onerous. Through the Baseline Cyber Security Controls for SMOs, the Canadian Centre for Cyber Security (Cyber Centre) has developed a set of low‑cost, low‑burden security controls for small- and medium‑sized organizations (SMOs), a catch‑all classification that include SMEs and other organizations like non‑profits and charities. These foundational cyber defence best practices are easy to implement and help SMOs thwart cyber threat actors, reduce exposure to cyber attacks, and get the most out of their cyber security investments.
While all 13 baseline controls developed by the Cyber Centre help organizations reduce the risk of cyber security incidents, below are summaries of four baseline controls that should be top of mind. SMOs should refer to the full document for more complete information. To be sure, cyber security needs are different for each organization and policies should be customized accordingly.
Develop an incident response plan
- Organizations should have a basic plan for how to respond to incidents of varying severity. If an organization cannot manage some types of incidents on its own, the organization should have a plan for what it will do.
- Organizations should have a written incident response plan that details who is responsible for handling incidents including any relevant contact information for communicating to external parties, stakeholders and regulators. Organizations should have an up‑to‑date hard copy version of this plan available for situations where soft copies are not available.
- Following a risk assessment and adoption of a risk mitigation strategy, organizations should consider purchasing a cyber security insurance policy that includes coverage for incident response and recovery activities or provide rationale for not purchasing one.
Automatically patch operating systems and applications
- Organizations should enable automatic patching for all software and hardware or establish full vulnerability and patch management solutions.
- Organizations should conduct risk assessment activities as to whether to replace any software and hardware that are not capable of automatic updates. If the organization chooses to keep such devices, they should have a business process to ensure regular manual updates.
Use strong user authentication
- Organizations should implement multi‑factor authentication wherever possible and document all instances where they make the business decision not to do so. Organizations should require multi‑factor authentication for important accounts such as financial accounts, system administrators, cloud administration, privileged users, and senior executives.
- Organizations should only enforce password changes on suspicion or evidence of compromise.
- Organizations should have clear policies on password length and reuse, the use of password managers and if, when, and how users can physically write down and securely store a password.
Back up and encrypt data
- Organizations should back up systems that contain essential business information and ensure that recovery mechanisms effectively and efficiently restore these systems from back‑ups. Organizations should consider storing backups offline at a secure offsite location or provide a rationale for not doing so.
- Organizations should securely store backups in an encrypted state and restrict access to them to those who must access them for the testing or use of restoration activities. Long term backups (e.g. weekly backups) must be stored offline, but frequent backups (e.g. daily backups) may be stored online.
Additional resources to strengthen cyber resilience
Canadian Shield
Developed by the Canadian Internet Registration Authority, in collaboration with the Cyber Centre, Canadian Shield is free Software as a Service solution for SMEs that blocks sites deemed as malicious.
DMARC Implementation Guidance
The Cyber Centre’s guidance on Domain‑based Message Authentication, Reporting & Conformance (DMARC) helps to counter phishing and Business Email Compromise, as well as protect the brand reputation of the organization.
Cyber Security Toolkit for SMEs
Developed by the Canadian Bankers Association, in collaboration with the Cyber Centre, the Small Business Cyber Security Toolkit helps business owners and managers better protect themselves from the most common cyber threats.
Password Guidance
Actionable information developed by the Cyber Centre on how to choose strong and effective passwords to help avoid credential stuffing.
CyberSecure Canada
A voluntary cyber security certification program administered by the Department of Innovation, Science and Economic Development, with guidance provided by the Cyber Centre, that helps SMOs achieve a baseline level of cyber security.
i Statistics Canada. "Key Small Business Statistics – January 2019" www.ic.gc.ca/eic/site/061.nsf/eng/h_03090.html#point1-1
ii An SME is defined as a business whose number of employees range from 1-99 (small) and 100-499 (medium)
iii Statistics Canada. "Impact of cybercrime on Canadian businesses, 2017" www150.statcan.gc.ca/n1/daily-quotidien/181015/dq181015a-eng.htm